Facepalm: While we’ve seen plenty of instances of fraudulent or malware-packed apps sneaking their way onto Google’s Play Store, it’s less of a common sight on Apple’s App Store, something the Cupertino company often points out. However, there are a few malicious programs that circumvent its approval process, including an app masquerading as the popular password manager LastPass.
LastPass posted a message on its website yesterday warning that a fraudulent app attempting to impersonate the password manager’s mobile application was available on the Apple App Store.
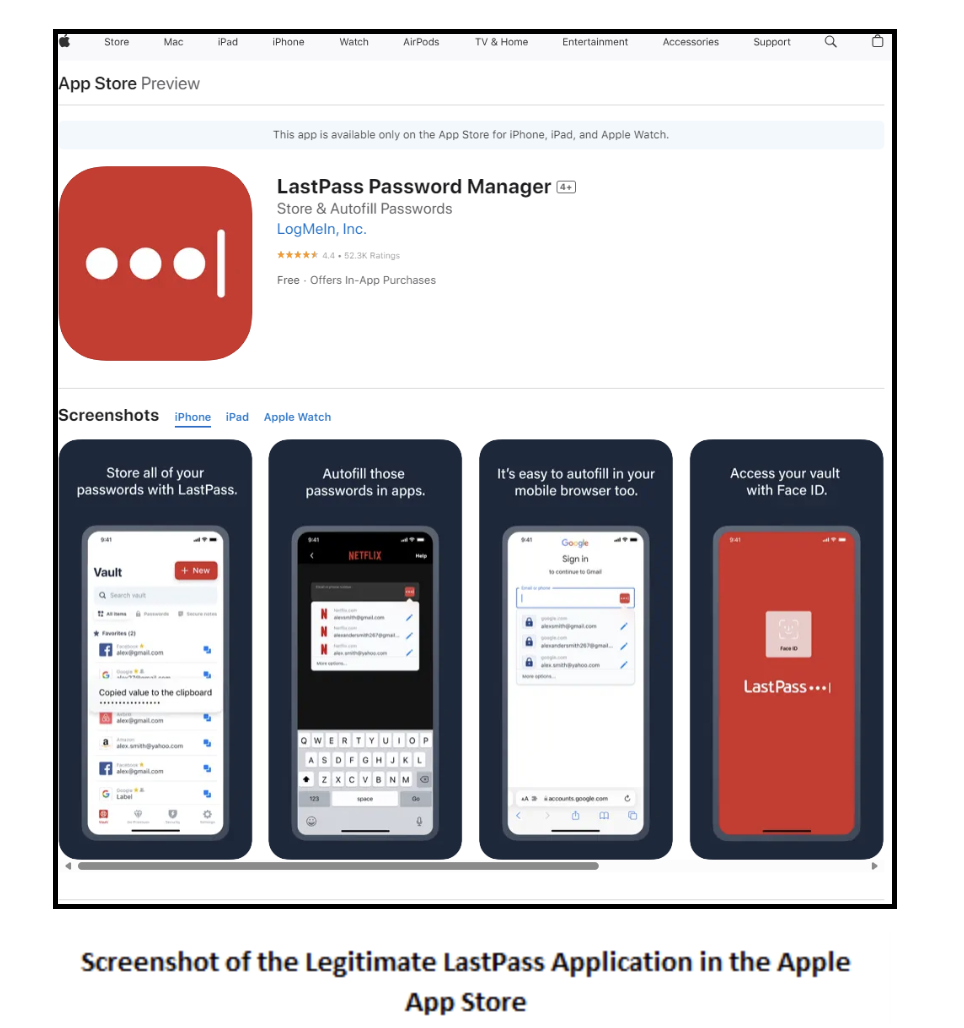
The app in question was called “LassPass Password Manager,” which should have raised suspicions, and listed Parvati Patel as the developer instead of owner LogMeIn. The app also attempted to copy elements of LastPass’ branding, logo, and user interface.
LastPass’ Senior Principal Intelligence Analyst, Mike Kosak, wrote. “We are raising this to our customers’ attention to avoid potential confusion and/or loss of personal data.”
Beyond the misspelling in the name, there were plenty of other spelling mistakes in the app’s description that made it stand out as a fake, making it all the more surprising that it escaped Apple’s submission checks.
The app was available for weeks before being taken down after the real LastPass highlighted it as a fake. It’s unclear if this was done by Apple – LastPass informed Apple the day after posting the warning – or the developer. There had been another app on the store from the same dev, but that has also been removed.
News of an obviously fake app making its way onto the App Store comes at a bad time for Apple. The company is currently arguing that the EU’s Digital Markets Act (DMA), which allows third-party app stores to host iOS apps, will compromise iPhone users’ safety and “bring new risks.” Like fake apps, presumably.
Exactly what LassPass did when it was installed on a device is unclear, though there appears to be no direct link to LastPass so user credentials were not copied from the official password manager. It’s likely that the developer was stealing sensitive personal information such as passwords, email and physical addresses, and payment card details – the app included a subscription option.